
INTRODUCTION
This blog shares the findings of Cylera Labs threat intelligence researchers, who first found a link between Kwampirs and Shamoon following the 2018 Symantec discovery of Kwampirs and Orangeworm. Now, new evidence is being publicly presented by Cylera Labs, giving medium-high confidence of attribution for Kwampirs.
SUMMARY OF SHAMOON
Shamoon is believed to be inspired by malware that was first deployed against the Iranian oil industry in April 2012 and dubbed “Wiper” by its own authors. Shamoon malware steals information, includes a destructive wiper module, and reports infection information back to the attackers. It renders infected computers useless, and data is not recoverable.
On August 15, 2012, during Ramadan holidays, the state-owned oil company, Saudi Aramco was attacked by Shamoon, aka, DistTrack. The “dropper” was delivered in an email opened by an IT worker with privileged access. Spreading rapidly through the network, business was brought to an immediate halt, and it took months to fully recover. Ultimately, Saudi Aramco had to replace 35,000 affected computers, causing global scarcity and price hikes in the world supply of computer components at the time. Shamoon was also used against petrochemical firm RasGas in November 2012.
After years of dormancy, Shamoon campaigns using updated wiper variants, resurfaced multiple times around the world, each time with devastating consequences - (November 2016, January 2017, and December 2018.)
FROM 2018 TO NOW
In April 2018, the world was experiencing Kwampirs, a malware remote access trojan (RAT) which provided “back door” access to systems it compromised. Symantec blogged details of the attacks coming from a group dubbed Orangeworm. At the time, they did not consider Orangeworm a nation-state actor, nor did other research organizations doing similar analysis.
__________________________________________________________________________________________
“While Orangeworm is known to have been active for at least several years, we do not believe that the group bears any hallmarks of a state-sponsored actor - - it is likely the work of an individual or small group of individuals. There are currently no technical or operational indicators to ascertain the origin of the group.” - April 23, 2018, Symantec Blog
__________________________________________________________________________________________
Symantec found evidence that since 2015, Orangeworm had been targeting global critical infrastructure sectors, including healthcare, and related supply chains, using Kwampirs. As a trojan, Kwampirs installed a back door on compromised systems and stealthily maintained access over time, exploring computers and networks of their victims.
Industry Sectors of Known Kwampirs Victims
(as of April 2018, Symantec)
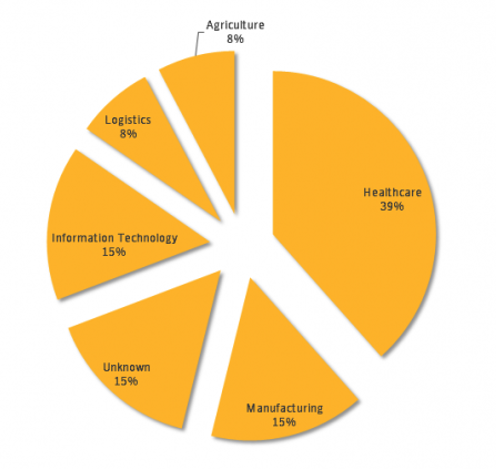
Fig 1. Industry sector data on known and unknown Kwampirs victims. At the time, the highest proportion of victims (40 percent) were in the healthcare sector. (April 2018, Symantec)
CYLERA's EARLY FINDINGS
Cylera Labs researchers then began an exhaustive investigation in 2018 on Orangeworm attribution, intentions, and motivation within healthcare supply chains, and its Kwampirs malware components in August 2018. During investigation, Kwampirs was even seen on X-ray, CT, and MRI machines.

Three months later, while monitoring for new campaigns, Cylera researchers found a Kwampirs Command and Control server which was intermittently active, and had a vulnerability that allowed our researchers to gather victim telemetry. A sinkhole was created for this campaign.
PUBLIC DISCLOSURE - 2019
When Cylera first discovered promising similarities between Shamoon and Kwampirs in 2018-2019, it was relevant to share with the community. Our first public disclosure of code samples and linking similarities was at the December 2019 XIII STIC conference in Madrid, presented by Pablo Ricón Crespo, vice president of cybersecurity and lead researcher at Cylera. At the time, the presentation shared first samples of the investigation with artifacts and linkage, showing a lot of potential, but we knew more research would be warranted.
Then, from January through March 2020 and immediately following the XIII STIC presentation, the U.S. Federal Bureau of Investigation (FBI) issued successive warning notifications on Kwampirs, and continued to press urgently for defensive actions to be taken in critical infrastructure sectors, healthcare, and in related supply chains:
Throughout the spring of 2020, a flurry of indicators of compromise (IoCs), vendors offering help, reports, code samples and mitigations were published around the industry related to Kwampirs and how to remediate and reinforce defenses.
ATTRIBUTION
In the 2012 attack against Aramco, the group claiming responsibility was the “Cutting Sword of Justice,” a group believed to be supported by Iran, though denied by Iranian leadership.
By December 2018, a ZDNet article cited McAfee's Advanced Threat Research team attributing Shamoon and recent activity to Iranian hacker group APT33 “or a group masquerading as APT33.” In security circles, Shamoon is believed to be linked with the Iranian attack groups APT33 and APT34.
Given that Shamoon 1 and 2 are allegedly Iranian APT, then Kwampirs would also be an Iranian APT too, targeting ICS, public and private healthcare institutions, and supply chains for critical infrastructure industries since at least 2015, as also stated in the FBI notifications.
SUMMARY
Fast-forwarding to now, while Kwampirs and Shamoon haven't been prevalent in the threat landscape, it's been seen time and again that older attacks can resurface. Examples like Conficker, seem to continue to live on: 14-year old code resurfacing and compromising organizations. In this case, there have been updated malware campaigns with new elements to differentiate each wave, like Shamoon/Kwampirs and others.
Our research evidence shows the identification of co-evolution between both Shamoon and Kwampirs malware families during the known timeline. Our technical blog on this topic and detailed analysis report contain a differential analysis of all the component versions of both families, known as the “reporters,” which allowed us to understand the coevolution in the same timeline.
If Kwampirs is based on the original Shamoon, and Shamoon 2 and 3 campaign codes are based on Kwampirs, with both statements supported by our findings, then the authors of Kwampirs would potentially be the same as the authors of Shamoon or must have a very strong relationship, as has been seen over the course of many years.
We believe with medium-high confidence that the evidence available supports attribution for Kwampirs to Iranian threat actors, and that healthcare and critical infrastructures, plus supply chains relevant to healthcare and other sectors need to be on guard for potential further updates and destructive reuse.
For more detailed information, please reference the Kwampirs-ShamoonTechnical Blog, and the in-depth Cylera Labs Kwampirs Shamoon Technical Report.
